One pattern. Five sectors.
The underlying failure is structurally identical: data exists but lives in silos. Detection happens too late. Coordination fails across agencies that each hold a fragment of the picture. The architecture is domain-agnostic. What changes is the entity model and policy logic.
Operational intelligence use cases follow a structurally identical pattern: data exists but lives in silos, detection happens too late, and coordination fails across teams that each hold a fragment of the picture. The architecture is domain-agnostic — what changes is the entity model and the policy logic.
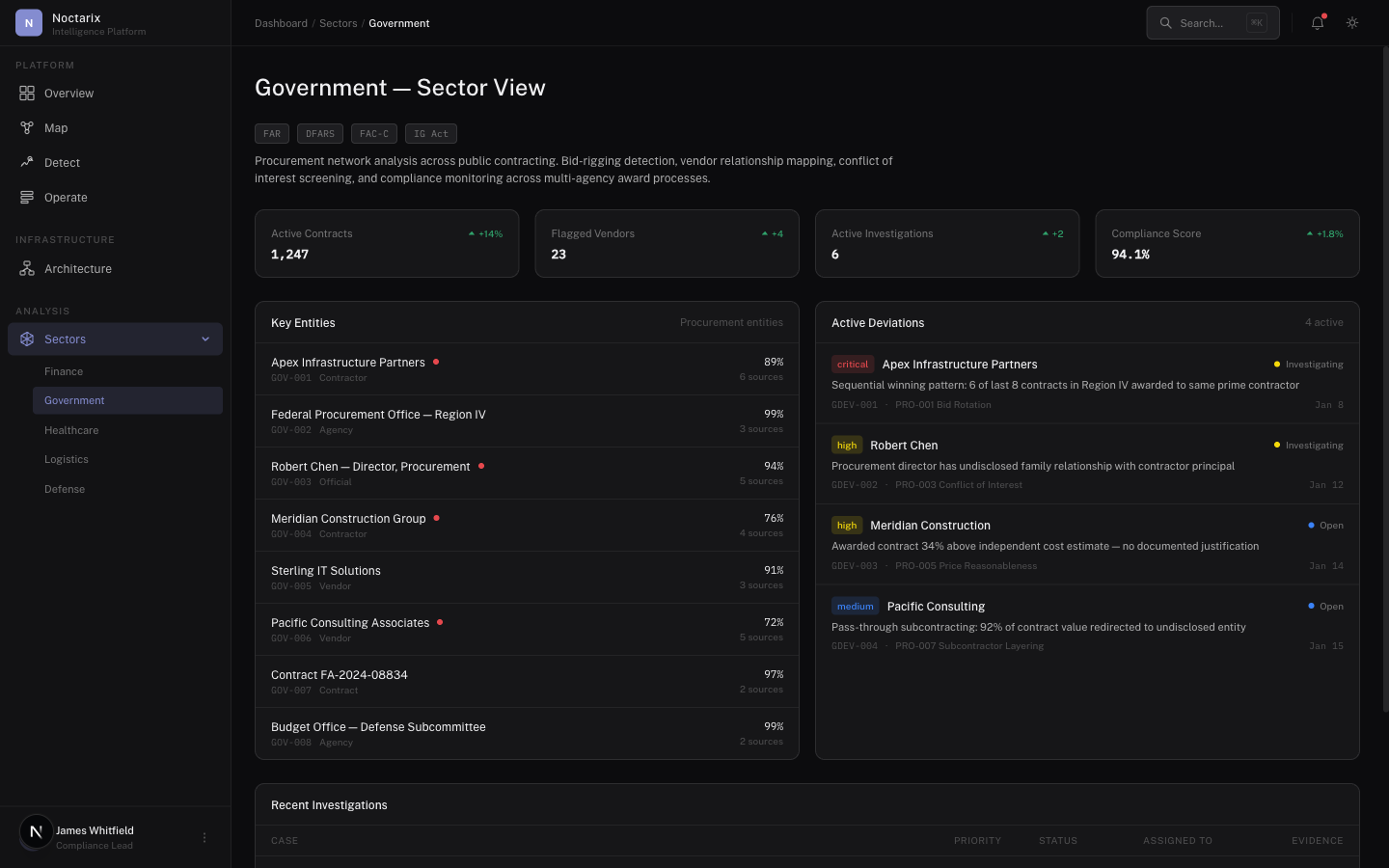
Procurement integrity and fraud networks
Governments lose billions — not because evidence doesn't exist, but because it's scattered. Procurement systems, vendor registries, customs records, banking reports, field audits. Each agency sees its own fragment.
Noctarix maps vendors, directors, addresses, bank accounts, contracts, and payments into a single graph.
Deviations detected
- Repeated award patterns inconsistent with procurement policy
- Vendor networks sharing directors or addresses
- Contract splitting across approval thresholds
- Payments inconsistent with delivery evidence
Investigations produce evidence packages for auditors and enforcement — not dashboards for executives to ignore.
Cross-agency coordination
Some failures are coordination failures: agencies each see one piece. Noctarix provides shared operational visibility with controlled access boundaries.
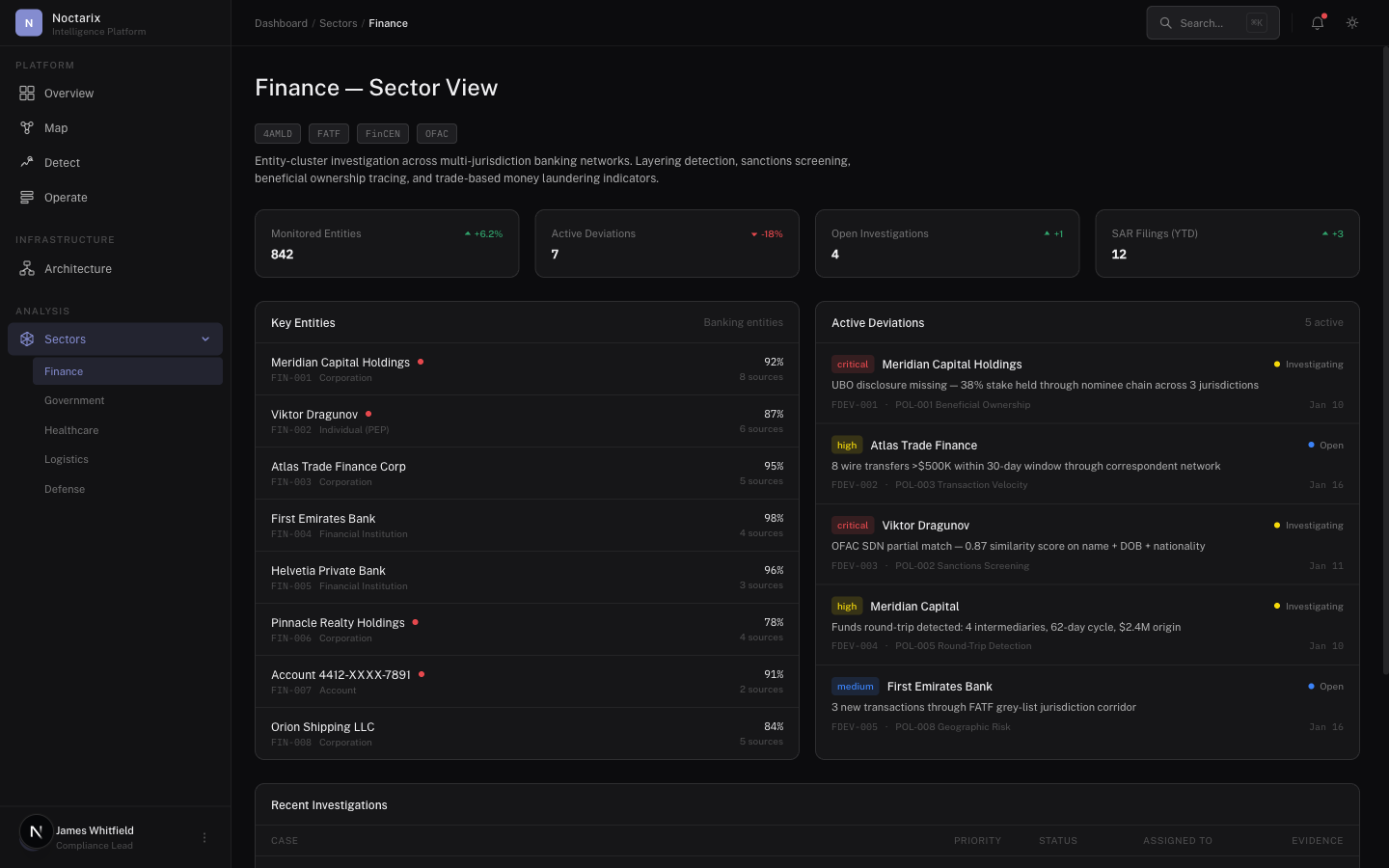
AML and transaction monitoring
Banks spend heavily on manual triage because entity resolution across systems remains expensive and error-prone. Noctarix reduces that cost by mapping accounts, customers, counterparties, devices, addresses, and transactions into a single investigation graph.
Deviations detected
- Suspicious transaction clusters across linked entities
- Relationship patterns invisible in tabular monitoring
- Deviations from expected KYC/EDD process steps
Structured SAR-ready evidence with full provenance.
Compliance operations
Convert policy requirements into enforceable checks. Missing documentation, incomplete workflows, breached thresholds — flagged automatically, investigated with trace.
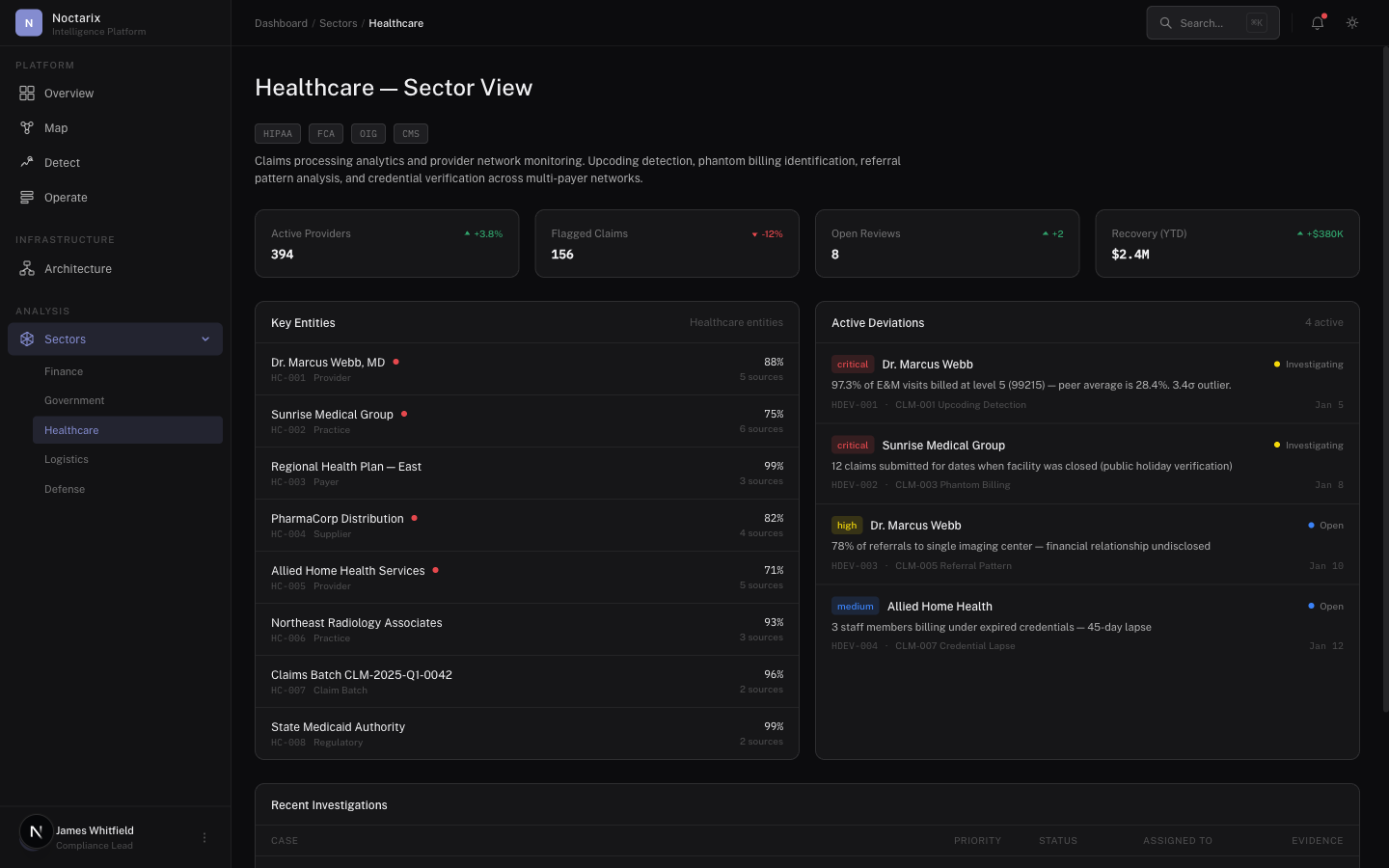
Claims integrity and supply chain
Claims fraud depends on network behavior — provider clusters, patient overlaps, billing anomalies across time. Not isolated transactions.
Noctarix maps providers, claims, procedures, pharmacies, and payer relationships.
Deviations detected
- Deviation from expected authorization and documentation flow
- Unusual provider networks and referral loops
- Supply chain inconsistencies correlated with claims behavior
Pharmaceutical supply chain
Distributors, warehouses, hospital inventory, billing — events across the chain mapped into a coherent picture. Missing custody steps, inconsistent batch lineage, abnormal routing.
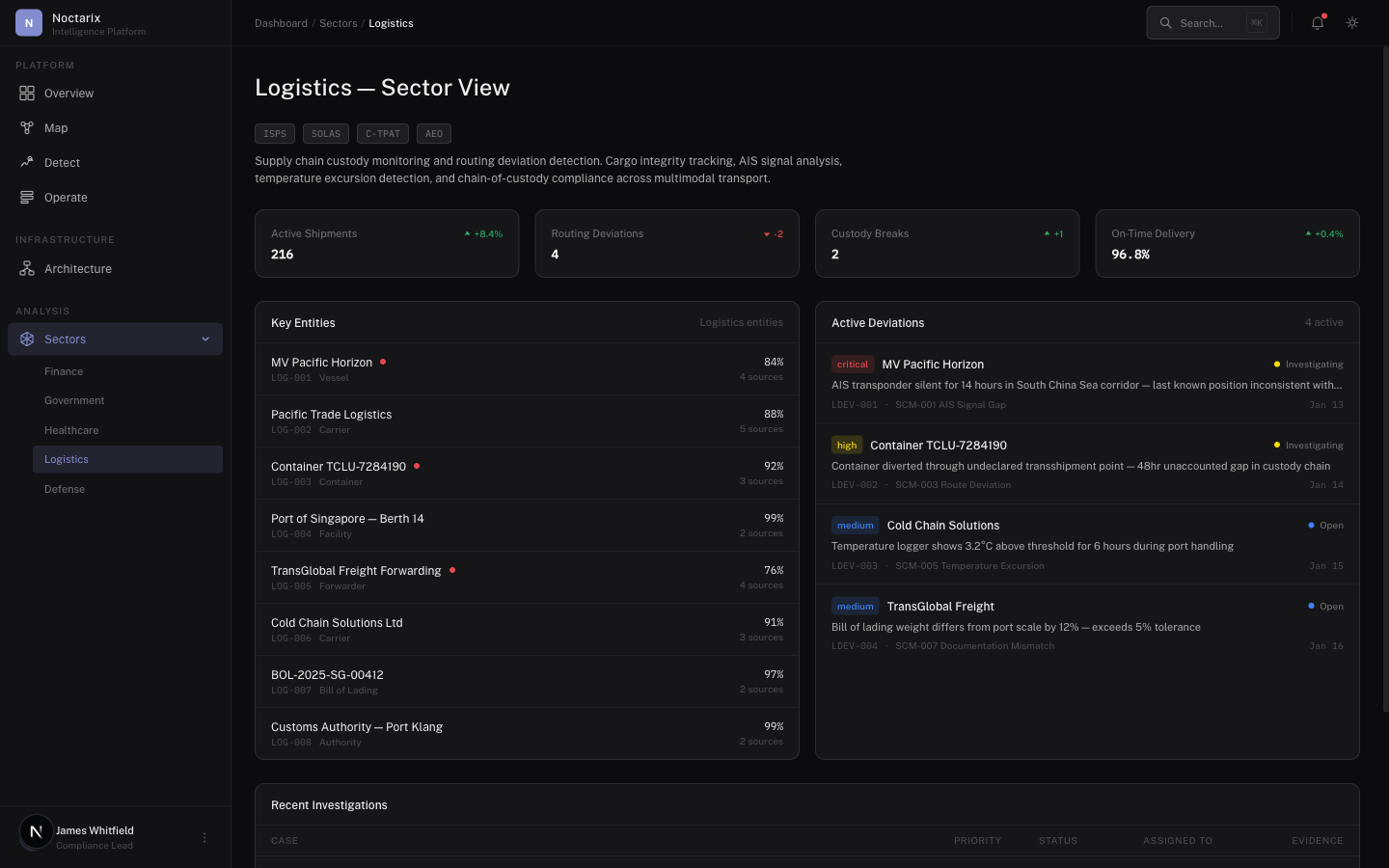
Exceptions are where logistics systems fail
Logistics is strong at planned movement and weak at everything else. Delays, diversions, inventory mismatch, suspicious routing — these are the signals that matter.
Deviations detected
- Route deviations inconsistent with declared constraints
- Repeated exceptions tied to shared entities (drivers, depots, vendors)
- Custody breaks across handoffs
Investigations build provenance-backed evidence that supports corrective action and accountability — not just exception reports.
Correlation and action under time constraints
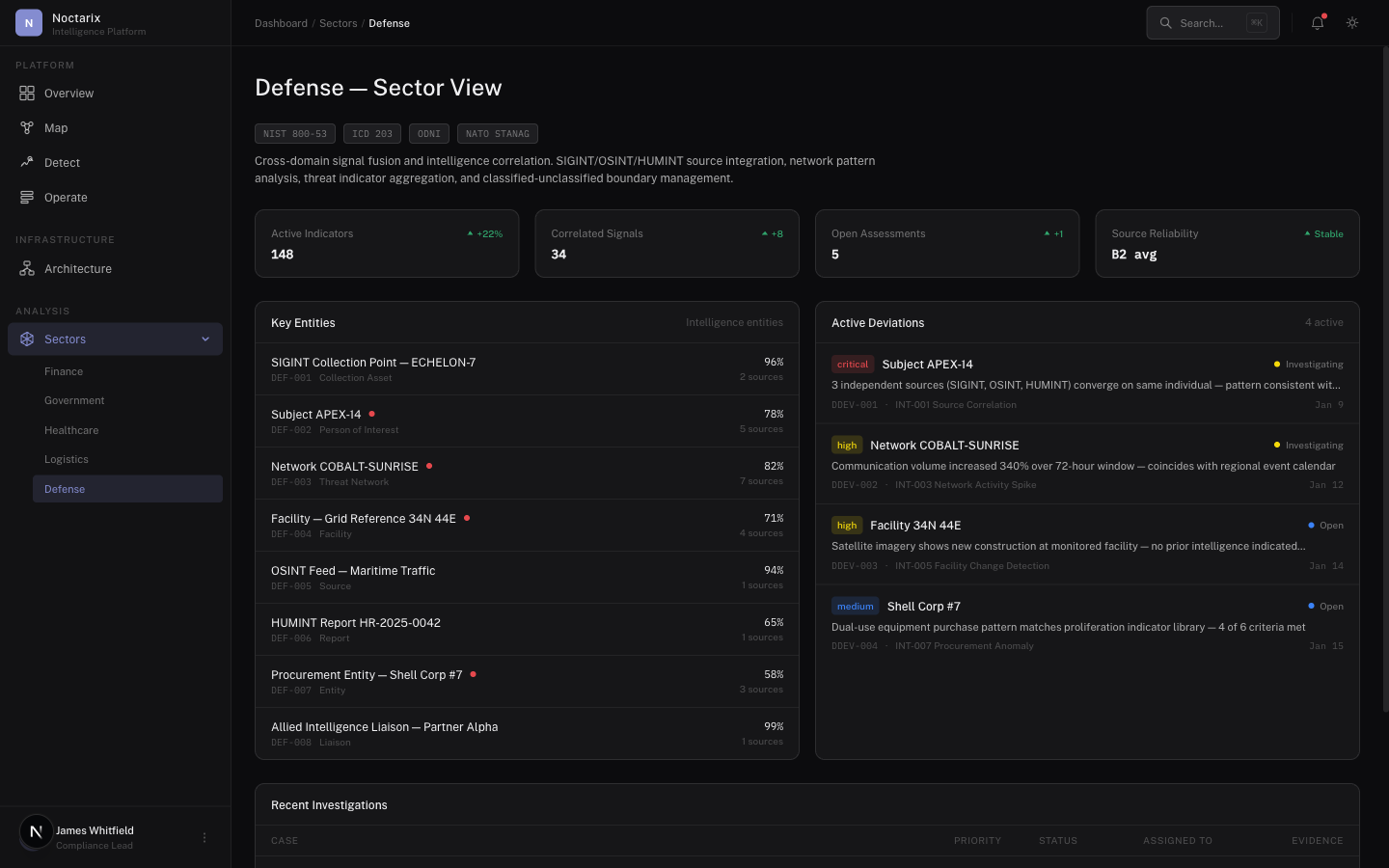
The sources already exist — signals, reports, logistics data, intercepts, imagery metadata. The problem isn't volume. It's connecting them fast enough to act.
What Noctarix provides
- Entity resolution across source types — one identity, however many aliases
- Link analysis and network mapping — see the structure, not just the nodes
- Deviation detection against expected operating patterns — know when something breaks before it escalates
- Bounded investigative playbooks with full trace — every action recorded, every source cited
Speed, accuracy, and accountability — correlated intelligence that operators can act on and auditors can verify.
Logistics coordination
Readiness fails when parts, maintenance cycles, and inventory don't match. Graph + deviation detection exposes systemic causes, not symptoms.
Scope a pilot
We respond within one business day to schedule a 30-minute briefing.